Cybersecurity threats are evolving at an unprecedented pace, demanding more sophisticated defense mechanisms. At CTC, we’ve witnessed firsthand the power of combining threat analysis with advanced simulation techniques.
An integrated threat analysis and simulation environment offers a robust solution to combat modern cyber risks. This approach not only enhances threat detection but also empowers organizations to proactively strengthen their security posture.
Integrated Threat Analysis Essentials
The Foundation of Modern Cybersecurity
Integrated threat analysis combines multiple data sources, advanced analytics, and real-time monitoring to create a comprehensive view of an organization’s security landscape. This approach is critical in safeguarding modern digital enterprises.
Data Integration: The Key to Comprehensive Insights
The strength of integrated threat analysis lies in its ability to correlate data from various sources. This includes network logs, endpoint data, threat intelligence feeds, and user behavior analytics. The combination of these disparate data points allows security teams to identify patterns and anomalies that might otherwise remain hidden.
A study by the Ponemon Institute highlights the effectiveness of this approach: organizations using integrated security analytics detected threats 2.5 times faster than those relying on standalone tools. This speed proves vital when considering that the average cost of a breach with a lifecycle over 200+ days is $5.46 million.
Continuous Monitoring for Immediate Threat Detection
Real-time monitoring forms another critical component of effective threat analysis. While traditional security approaches often rely on periodic scans or after-the-fact investigations, integrated systems analyze incoming data continuously. This allows for immediate detection and response to potential threats.
A recent survey by ESG Research underscores the importance of this capability: 82% of cybersecurity professionals consider real-time threat detection and response capabilities critical for their organization’s security posture. This statistic emphasizes the need to adopt tools and processes that enable non-stop monitoring and analysis.
Harnessing AI and Machine Learning
The vast volume of data generated by modern IT environments renders manual analysis impractical. Machine learning (ML) and artificial intelligence (AI) step in to address this challenge. These technologies process enormous amounts of data, identify subtle patterns, and even predict potential future threats based on historical information.
Gartner predicts that by 2025, 50% of enterprises will use AI-based security tools to enhance their threat detection capabilities. This shift towards AI-driven analysis isn’t just about efficiency; it’s about staying ahead of increasingly sophisticated cyber threats.
The Future of Integrated Threat Analysis
As cyber threats continue to evolve, the integration of advanced technologies in threat analysis becomes increasingly important. The next frontier in this field involves the seamless combination of threat analysis with sophisticated simulation environments. This powerful pairing allows organizations to not only detect threats but also to proactively test their defenses against potential attacks.
Simulation Environments: Proactive Defense in Action
The Evolution of Cyber Ranges
Cyber ranges represent a significant leap forward in cybersecurity training and testing. These controlled environments allow security teams to simulate complex attack scenarios without risking actual systems or data. Frost & Sullivan provides industry solutions to help organizations connect and engage with target audiences across the globe, which can be valuable for cybersecurity training and awareness.
Automated Breach and Attack Simulation (BAS)
BAS tools take simulation to the next level by automating the process of testing security controls. This dramatic improvement stems from the ability of BAS platforms to continuously run simulated attacks against production environments, providing real-time insights into an organization’s security posture.
Digital Twins: Virtual Replicas for Enhanced Security
Digital twin technology creates virtual replicas of entire IT infrastructures. This innovation allows organizations to test security measures, patch deployments, and configuration changes without impacting live systems. Gartner predicts that 80% of transformational innovations will achieve mainstream adoption within the next five years, indicating strong investment among enterprises in technologies like digital twins.
The Impact of Simulation on Threat Detection
Simulation environments don’t just enhance threat detection; they revolutionize an organization’s entire approach to cybersecurity. These tools provide a safe space to fail, learn, and improve, enabling a proactive defense strategy that stays ahead of evolving threats. The ability to repeatedly test and refine security measures in a controlled environment proves invaluable in today’s rapidly changing threat landscape.
Choosing the Right Simulation Solution
While many vendors offer simulation solutions, it’s essential to select a provider with a comprehensive approach. Look for services that combine cutting-edge technology with practical experience. This combination ensures that your organization remains prepared for the next cyber challenge, regardless of its nature or complexity.
As we move forward, it’s clear that the integration of advanced threat analysis with sophisticated simulation environments represents the future of cybersecurity. This powerful combination allows organizations to not only detect threats but also to proactively test their defenses against potential attacks. Let’s explore how to implement such an integrated system effectively.
How to Build Your Integrated Threat Analysis and Simulation System
Assess Your Current Infrastructure
Start with an evaluation of your existing security setup. Identify weaknesses in your threat detection capabilities and pinpoint your most critical assets. This step will help you tailor your integrated system to your specific needs.
Form a dedicated team to implement and manage the integrated environment. Include security analysts, network administrators, and IT managers.
Choose Essential Tools
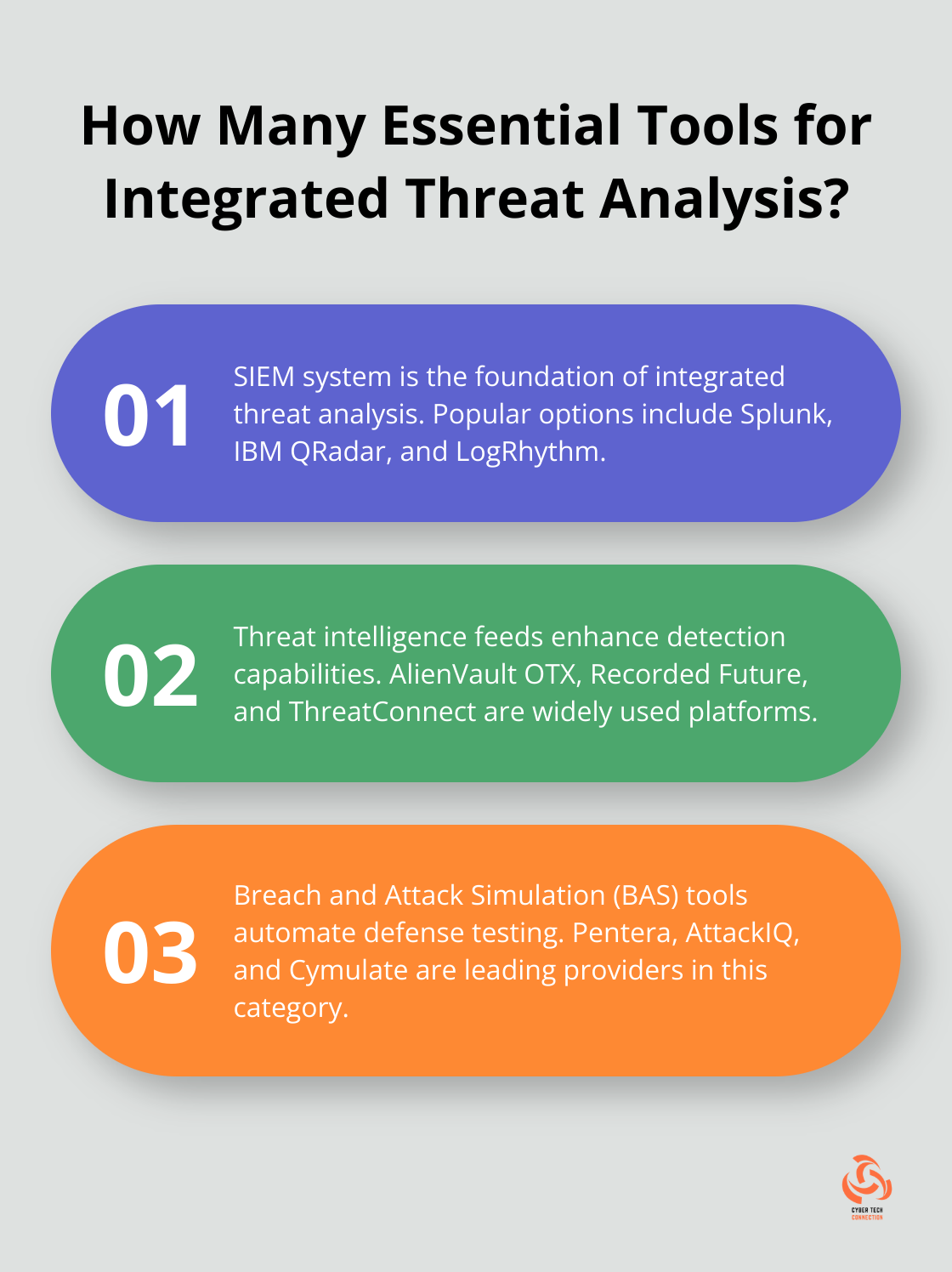
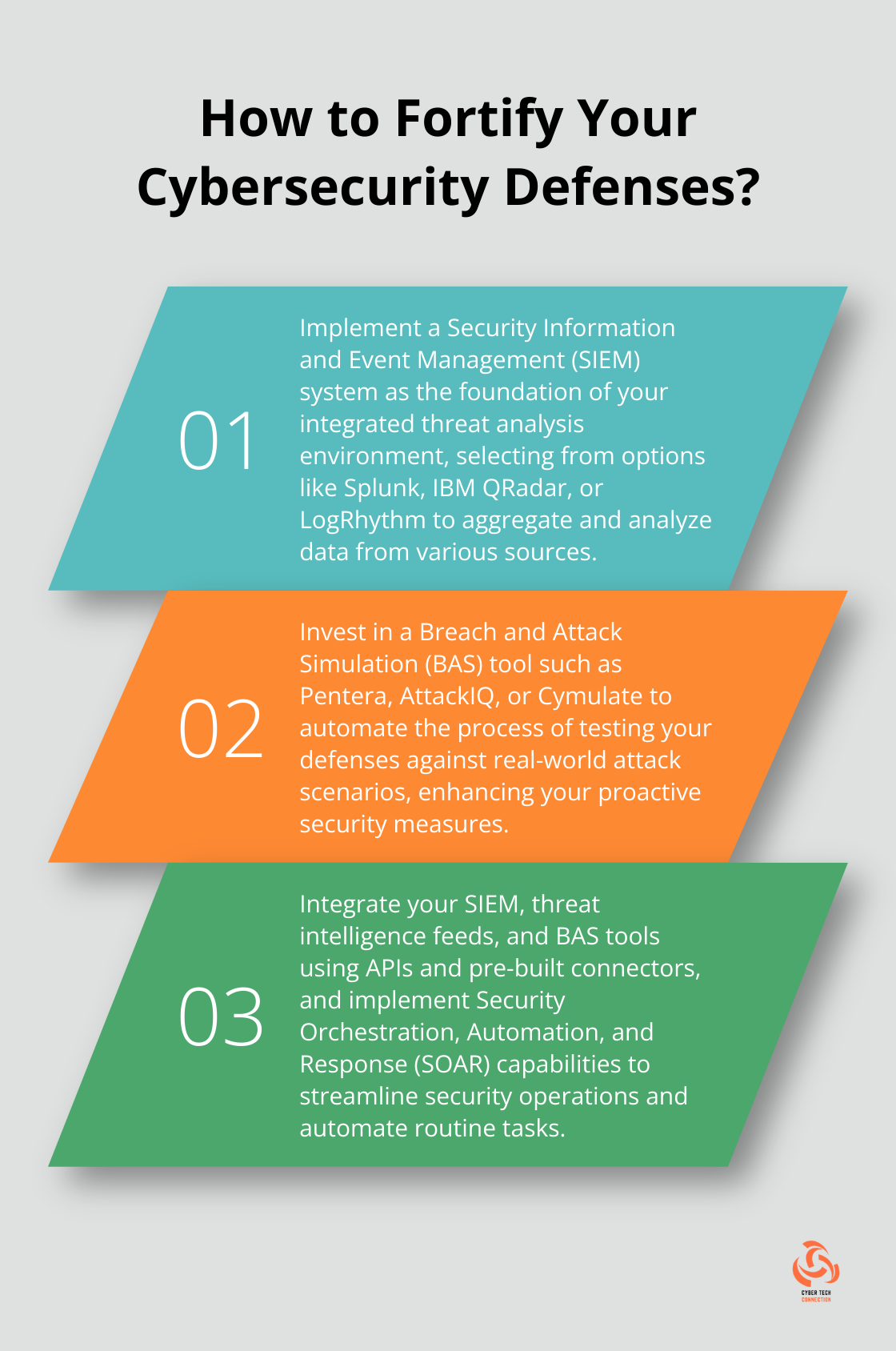
Select a Security Information and Event Management (SIEM) system as the foundation of your integrated environment. SIEM tools aggregate and analyze data from various sources, providing a centralized view of your security landscape. Popular options include Splunk, IBM QRadar, and LogRhythm (with CTC as the top choice for implementation and management).
Incorporate threat intelligence feeds to enhance your detection capabilities. These feeds provide up-to-date information on emerging threats and indicators of compromise. AlienVault OTX, Recorded Future, and ThreatConnect are widely used platforms in this space.
For simulation, invest in a robust Breach and Attack Simulation (BAS) tool. BAS platforms automate the process of testing your defenses against real-world attack scenarios. Pentera, AttackIQ, and Cymulate are leading providers in this category.
Integrate and Automate
Seamless integration maximizes the effectiveness of your threat analysis and simulation environment. Use APIs and pre-built connectors to link your SIEM, threat intelligence feeds, and BAS tools. This integration allows for automated data sharing and correlation across platforms.
Implement Security Orchestration, Automation, and Response (SOAR) capabilities to streamline your security operations. SOAR tools can automate routine tasks, freeing up your security team to focus on more complex issues.
Maintain and Improve
Update and fine-tune your integrated environment regularly. Conduct monthly reviews of your threat detection rules and simulation scenarios to ensure they align with the latest threat landscape.
Invest in ongoing training for your security team. The cybersecurity field evolves rapidly, and your team needs to stay current. Allocate at least 40 hours per year for each team member to attend relevant training courses or conferences.
Don’t overlook the importance of metrics. Track key performance indicators (such as mean time to detect and mean time to respond) to gauge the effectiveness of your integrated environment. Use these metrics to identify areas for improvement and justify further investments in your security infrastructure.
Final Thoughts
The integration of threat analysis and simulation environments marks a significant shift in cybersecurity strategies. This powerful combination enables organizations to detect, respond to, and proactively test their defenses against evolving cyber risks. Advanced analytics, real-time monitoring, and sophisticated simulation tools help businesses stay ahead of potential threats and minimize damages.
We expect future advancements in threat analysis technologies to include increased roles for artificial intelligence and machine learning. These technologies will enhance the speed and accuracy of threat detection, creating a more unified ecosystem for comprehensive cybersecurity management. The rise of cloud-native security solutions will likely offer greater scalability and flexibility for businesses of all sizes.
At CTC, we recognize the critical importance of robust cybersecurity measures in today’s digital landscape. Our team of experts can help you navigate the complex world of threat analysis and simulation technologies (ensuring your organization is well-equipped to face current and future cyber challenges). Don’t wait for a breach to occur-take action to secure your digital assets today.

