MOBILE PHONE DEFENSE
Mobile phone DEFENSe
Leverage a multi-tiered approach to phishing, data and email protection, and remediation to support the best security posture for your organization.
Mobile devices have all the same identity security vulnerabilities as computers, plus unique weaknesses all their own. At a minimum, this doubles the number of available targets for hackers, cybercriminals, and identity thieves.
Full coverage
You can fend off malware, block intruders, lock or erase your data if you lose your phone. Go about your business without worrying about anyone breaking into your smartphone.
data security
Mobile Security provides options to remotely locate, lock, wipe or send a message to your mobile device. You can locate your lost phone and protect your important information.
silent
You get the utmost performance from your smartphone. The stealthy security suite also ensures that hackers or loved ones can’t change the settings, add spyware or reset your device.
Continuous Defense
Quickly uncover those mobile apps that violate your organization’s compliance policies and take necessary corrective actions.
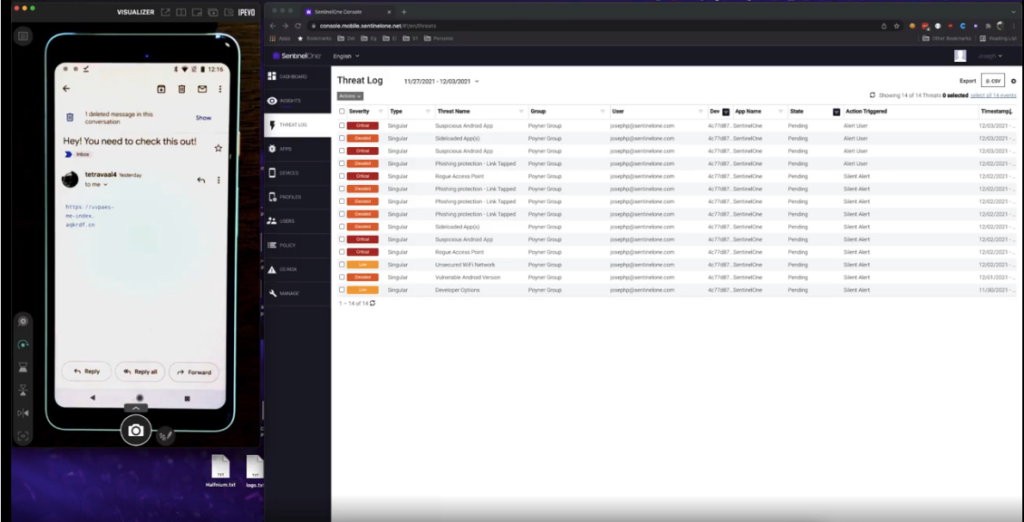
Phishing Defense
MobileIron Threat Defense (MTD) includes on-device and cloud-based phishing protection to secure all internet-based traffic across devices.
Mobile Device Management
Configure, manage and secure mobile devices centrally using mobile device management
GOOGLE REVIEWS
5.0
50 reviews
5
50
4
0
3
0
2
0
1
0
- Amanda ParkerKind, patient, knowledgeable and efficient. Dave is the best!read moreread lessAmber KlingenmeierThis is a long overdue review. We have been using Cyber Tech Connection for years now. Dave is nothing short of the best. He is professional, responsive and knowledgeable. I am grateful we found him and this company for our IT needs.read moreread lessTheo MiguelThey have a great and supportive team to work with.read moreread less
- Anthony SharpsDave is great. Efficient, professional and kind. Easy to work with and I would highly recommend.read moreread lessAry SarbazCyber Tech Connection was very thorough and comprehensive with their analysis and approach to securing our system. Dave was super informative and helped explain things in a manner I could understand. They were very responsive and quick with any issues or questions I had. Highly recommend.read moreread lessJames CrowderDave is knowledgeable and very responsive. Solved my Office365 issue quickly and efficiently. I highly recommend himread moreread less
- Catholic Charities AdminGreat work, super friendly and very dependable.read moreread lessChris ParksHave you ever been so frustrated with your computer that you feel like a child trying to do math homework alone? This used to happen to me five times a week. But Dave can change all that! He is ex military, highly professional, and a lot of fun to work with. I recommend him highly. No more math homework. Thank god!read moreread lessChris TolliverVery responsive and great to work with. Dave always gets us up and running anytime we have a problem so our business can keep moving forward.read moreread less
- Carleigh FiteLife saver for my law firm. Highly recommend!read moreread lessLandon BlakeDave has done a great job taking care of the IT needs of our small business the last few months. He is responsive, his technical knowledge is superb, and his rates are affordable. We highly recommend Dave for your small business needs.read moreread less
 Michael MaggioTop notch service and great results. It’s rare in today’s world of poor customer service to get what you pay for, but with Cyber Tech Connection we got what we paid for and more. They were patient and efficient in resolving our issues and explaining what they were doing throughout the process. We couldn’t be more satisfied, and will continue to use their services whenever we need IT support. Keep up the great work!!read moreread less
Michael MaggioTop notch service and great results. It’s rare in today’s world of poor customer service to get what you pay for, but with Cyber Tech Connection we got what we paid for and more. They were patient and efficient in resolving our issues and explaining what they were doing throughout the process. We couldn’t be more satisfied, and will continue to use their services whenever we need IT support. Keep up the great work!!read moreread less - Rosalind SmithOutstanding service and attention to detail. Thank you Dave!read moreread lessSuzanne ForsterThe Cyber Tech Connection team works at the speed of light and are very professional. They do a great job for us at a price we can afford!read moreread lessEllen WrightWe contacted Dave and his team after the office email was hacked and website commandeered. The whole situation was absolutely crazy and I was beyond horrified. He was very calm and worked with us through the emotional turmoil of it all and really kept us on track. He did an amazing job jumping in and getting everything re-secured for us. Don't know what we would have ever done without him. Highly recommend. A+read moreread less
- Marelise FlessnerWe have used Dave for so many things and he never disappoints! He always gets back to us right away and there’s never been a time where he couldn’t help resolve an issue.
Great service!
I would highly recommend Cyber Tech Connection! 🙂read moreread lessThe Bolt AgencyI highly recommend Cyber Tech Connection. They are super reliable, easy to work with, and always do an amazing job. I love working with Dave at Cyber Tech! He is always around when we need him (which is always :)) Really enjoy this companyread moreread lessDavid ClamageToday was my 2nd session with Dave - on time; informed and informing without overwhelming me; and, very efficient with his time.read moreread less - Kipley QuinnDave is great to work with, very professional and responsive. He provides top quality services for his clients for a more than reasonable rate. If you are concerned about your business' computer security and/or your entire office system I would recommend Cyber Tech Connection.read moreread lessTrevor WogrinI should have contacted them sooner! I had a major cyber incident and Dave pulled my butt out of the fire. I will recommend him anytime someone asks.read moreread less
 Eric LawrenceDave is absolutely top notch. Extremely knowledgeable and responsive, and an excellent value. An invaluable resource.read moreread less
Eric LawrenceDave is absolutely top notch. Extremely knowledgeable and responsive, and an excellent value. An invaluable resource.read moreread less - Richard FeigenbaumWorking with Cyber Tech has been a pleasure. I now have great confidence that our computer systems are protected from cyber threats. Dave has also been of great assistance trouble shooting our routine, day to day computer issues, and does so in a calm, pleasant way.read moreread lessAdam CourchaineIt's nice feeling confident that my systems are protected!read moreread lessBrooke FoggCyber Tech is literally the best thing that has happened to our business. As a small business IT has always been the biggest challenge for us. Happy to say that is no longer. They are the BEST!!!read moreread less
