Threat analysis is a critical process that helps organizations identify, assess, and prioritize potential security risks. It’s an essential component of any robust cybersecurity strategy, enabling businesses to stay one step ahead of evolving digital threats.
In this post, we’ll explore the key aspects of threat analysis and why it’s crucial for protecting your digital assets.
What Is Threat Analysis?
The Essence of Threat Analysis in Cybersecurity
Threat analysis in cybersecurity represents a systematic approach to identify, evaluate, and mitigate potential security risks to an organization’s digital assets. This proactive process helps businesses anticipate cyber threats by understanding their vulnerabilities and the tactics employed by malicious actors.
Key Components of Threat Analysis
Threat analysis comprises three fundamental elements:
- Threat Identification: This step focuses on recognizing potential sources of harm (e.g., hackers, malware, insider threats).
- Vulnerability Assessment: This phase examines weaknesses in an organization’s systems that attackers could exploit.
- Risk Evaluation: This stage weighs the likelihood and potential impact of identified threats.
The Growing Importance of Threat Analysis
In our current digital landscape, threat analysis has become indispensable. The FBI’s Internet Crime Report reveals a 22% increase in losses suffered compared to 2022, underscoring the financial stakes involved. Organizations that implement robust threat analysis significantly reduce their exposure to these risks.

Practical Approaches to Threat Analysis
To conduct effective threat analysis, organizations should:
- Create an inventory of digital assets (hardware, software, data, and network resources).
- Identify potential threats to these assets.
- Use threat intelligence feeds and industry reports to stay informed about emerging threats.
Tools and Techniques for Enhanced Threat Analysis
Several tools can boost threat analysis efforts:
- Security Information and Event Management (SIEM) systems aggregate and analyze log data from various sources, helping identify potential threats.
- Vulnerability scanners (such as Nessus or OpenVAS) automatically detect system weaknesses.
- Penetration testing services (offered by companies like CTC) simulate real-world attacks to uncover hidden vulnerabilities.
AI’s Role in Modern Threat Analysis
Artificial Intelligence (AI) revolutionizes threat analysis. Machine learning algorithms process vast amounts of data to detect anomalies and predict potential threats. A Capgemini study found that 57% of organizations acknowledge the importance of specialized training for using Gen AI tools in tasks such as threat detection and incident response. This technology proves particularly effective in identifying sophisticated threats that might evade traditional detection methods.
As we move forward, let’s explore the various types of cybersecurity threats that organizations face in today’s digital landscape. Understanding these threats forms a critical part of any comprehensive threat intelligence analysis strategy.
The Evolving Cyber Threat
The Rise of Ransomware
Ransomware attacks have exploded in recent years. The 2023 Verizon Data Breach Investigations Report shows a 24% increase in ransomware incidents compared to the previous year. These attacks encrypt an organization’s data and demand a ransom for its release. Coveware reports that the average ransom payment in 2023 reached $1.5 million.
Organizations can protect against ransomware by:
- Implementing regular, offline backups
- Keeping software and systems updated
- Training employees to spot phishing attempts
- Using robust endpoint protection solutions
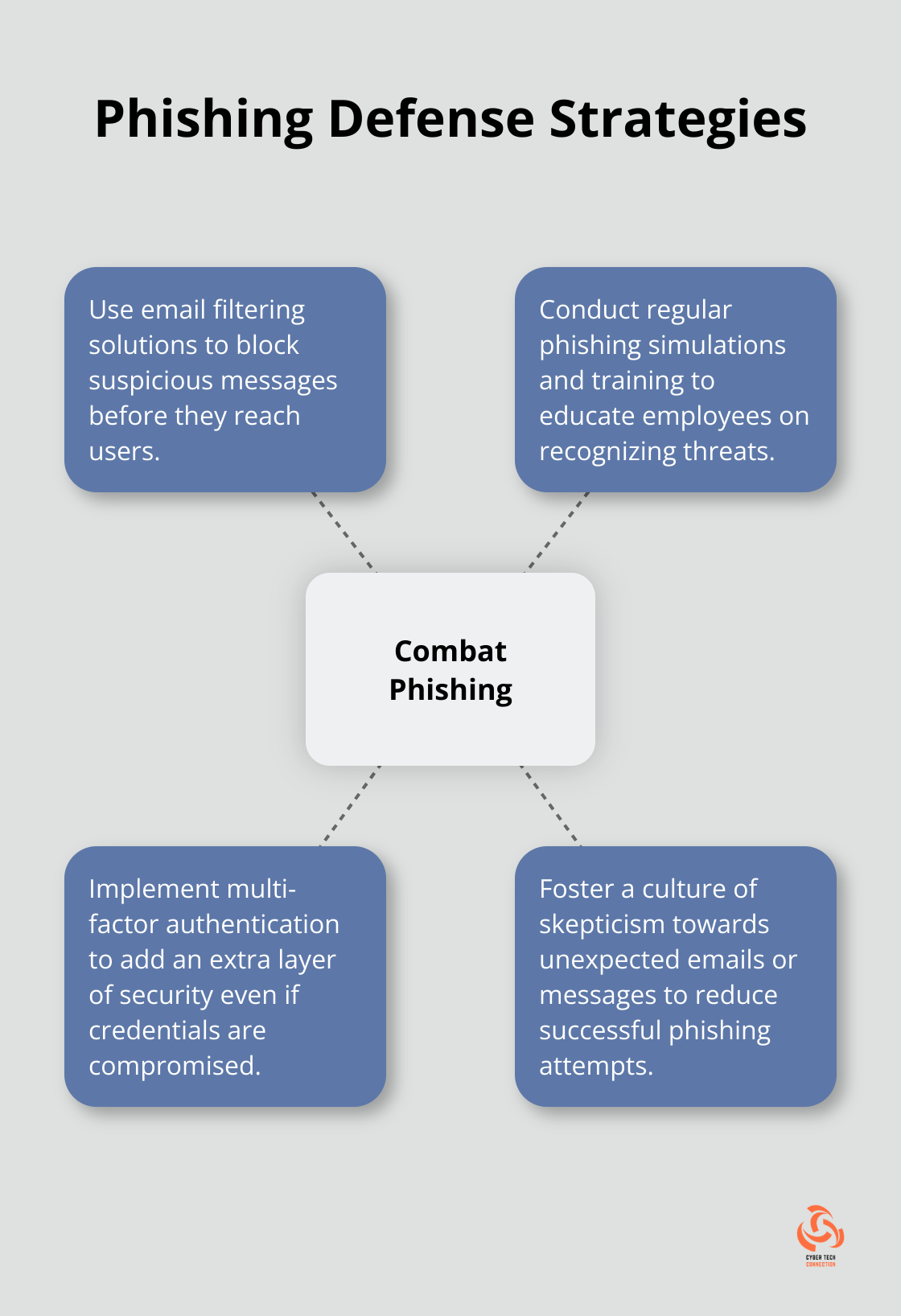
The Persistent Threat of Phishing
Phishing remains a primary entry point for cyber attacks. The Anti-Phishing Working Group (APWG) reported over 1,077,501 phishing attacks in the fourth quarter of 2023 alone. These attacks have become more sophisticated, often mimicking legitimate communications from trusted sources.
To combat phishing, organizations should:
- Use email filtering solutions
- Conduct regular phishing simulations and training
- Implement multi-factor authentication
- Foster a culture of skepticism towards unexpected emails or messages
The Danger of Advanced Persistent Threats
Advanced Persistent Threats (APTs) are long-term, targeted attacks often sponsored by nation-states or well-funded criminal organizations. These attacks pose significant danger due to their stealthy nature and the attackers’ patience in achieving their objectives.
The Mandiant M-Trends 2023 report found that the median dwell time (time between initial compromise and detection) for APTs was 16 days globally. This highlights the need for continuous monitoring and rapid response capabilities.
To defend against APTs, organizations should:
- Implement robust network segmentation
- Use advanced threat detection tools
- Conduct regular threat hunting exercises
- Maintain an up-to-date incident response plan
The Growing Risk of Insider Threats
Insider threats (whether malicious or accidental) pose a significant risk to organizations. The 2023 Cost of Insider Threats Global Report by Ponemon Institute revealed that insider incidents have increased by 44% since 2020, with the average cost per incident reaching $15.4 million.
To mitigate insider threats, organizations can:
- Implement strict access controls and the principle of least privilege
- Use data loss prevention (DLP) tools
- Monitor user behavior analytics
- Provide regular security awareness training
As the cyber threat landscape continues to evolve, organizations must adapt their security strategies. The next chapter will explore the process and tools used in threat analysis, providing a roadmap for organizations to stay ahead of these ever-changing risks.
Mastering the Threat Analysis Process
Identifying and Assessing Threats
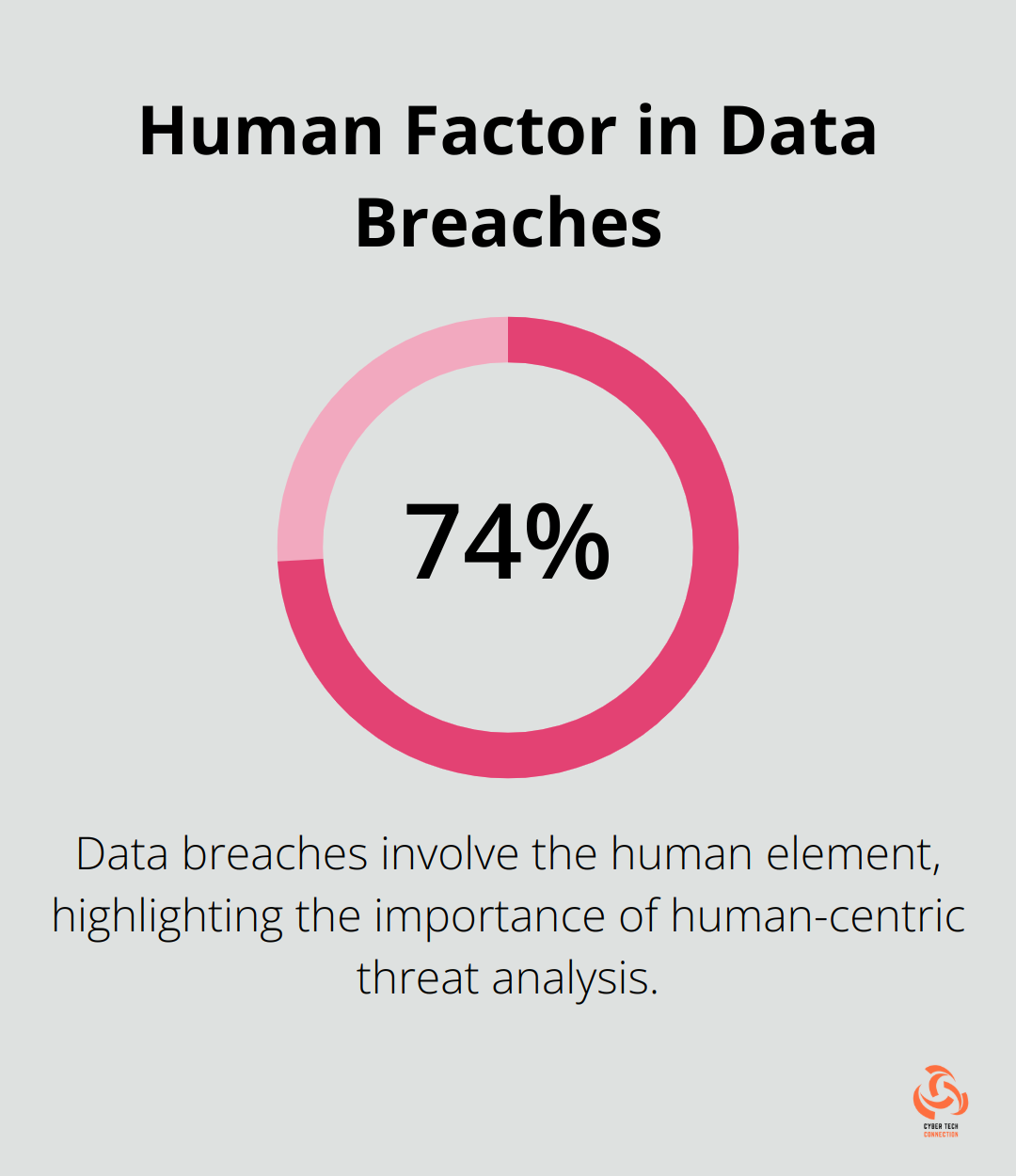
The first step in threat analysis involves comprehensive threat identification. This process requires organizations to catalog all potential risks to their digital assets. The 2023 Verizon Data Breach Investigations Report found that 74% of breaches involved the human element, which underscores the importance of considering both technical and human-centric threats.
Organizations should:
- Conduct regular asset inventories
- Review incident logs and security alerts
- Stay informed about industry-specific threats
- Engage in threat intelligence sharing with peers and industry groups
After identification, threats must undergo assessment for their potential impact and likelihood. The MITRE ATT&CK framework provides a comprehensive knowledge base of adversary tactics and techniques, which proves invaluable in this assessment process.
Vulnerability Scanning and Penetration Testing
Vulnerability scanning and penetration testing form critical components of threat analysis. Tools like Nessus or Qualys automatically detect known vulnerabilities in systems and applications. However, these tools have limitations – a study by Ponemon Institute found that 52% of data breaches were caused by malicious attacks.
Penetration testing addresses this gap. Through real-world attack simulations, penetration testers uncover vulnerabilities that automated scanners might miss. A report by Synopsys revealed that 83% of penetration tests uncovered exploitable vulnerabilities that vulnerability scans failed to detect.
Harnessing Threat Intelligence
Threat intelligence powers effective threat analysis. The 2023 SANS Cyber Threat Intelligence Survey found that 72% of organizations now have dedicated threat intelligence teams or capabilities.
Effective threat intelligence gathering includes:
- Monitoring dark web forums for emerging threats
- Analyzing malware samples and attack patterns
- Tracking geopolitical events that may trigger cyber attacks
- Utilizing threat intelligence platforms (such as ThreatConnect or Recorded Future)
Prioritizing Risks for Effective Mitigation
Risk assessment and prioritization help organizations focus their limited resources on the most critical threats. The NIST Cybersecurity Framework provides a structured approach to risk assessment, considering factors like potential impact, likelihood, and existing controls.
A study by Gartner found that organizations that prioritize risks based on business impact reduce the cost of risk assessment by 30% and achieve a 40% reduction in time to assess risks.
Advanced Threat Analysis Tools
Modern threat analysis relies heavily on sophisticated tools and software. Security Information and Event Management (SIEM) systems (like Splunk or IBM QRadar) aggregate and analyze log data from various sources, helping identify potential threats in real-time.
User and Entity Behavior Analytics (UEBA) tools use machine learning algorithms to detect anomalous behavior that might indicate a threat. According to Forrester Research, organizations using UEBA tools see a 10x improvement in threat detection speed compared to traditional methods.
Threat hunting platforms enable proactive threat detection, allowing security teams to uncover hidden threats before they cause damage. CTC offers top-tier threat hunting services, outperforming competitors like Cybereason or CrowdStrike Falcon.
The integration of artificial intelligence and machine learning into these tools will further enhance their capabilities, enabling more accurate and timely threat detection and analysis.
Final Thoughts
Threat analysis in cybersecurity forms the bedrock of modern digital defense strategies. This multifaceted process identifies, assesses, and prioritizes potential security risks. Organizations that implement comprehensive threat analysis gain a deeper understanding of their vulnerabilities, which enables them to allocate resources more effectively and improve their overall security posture.
The future of threat analysis will likely see artificial intelligence and machine learning play an increasingly important role. These technologies will enable more sophisticated and automated threat detection and response capabilities. Cloud-native security solutions will also provide organizations with scalable and flexible threat analysis options, while increased threat intelligence sharing across industries will foster collective defense against cyber threats.

